mn create-app example.micronaut.micronautguide --build=maven --lang=kotlinTable of Contents
- 1. Getting Started
- 2. What you will need
- 3. Solution
- 4. Writing the Application
- 5. OAuth 2.0 Dependency
- 6. Micronaut AWS Secrets Manager Dependency
- 7. Distributed Configuration
- 8. Create Secret
- 9. Controller
- 10. Logs
- 11. Running the Application
- 12. Generate a Micronaut Application Native Executable with GraalVM
- 13. Next steps
- 14. Help with the Micronaut Framework
Distributed Configuration with AWS Secrets Manager and the Micronaut Framework
Learn how to load your secrets from AWS Secrets Manager in your Micronaut application
Authors: Sergio del Amo
Micronaut Version: 3.9.2
1. Getting Started
In this guide, we will create a Micronaut application written in Kotlin.
2. What you will need
To complete this guide, you will need the following:
-
Some time on your hands
-
A decent text editor or IDE
-
JDK 1.8 or greater installed with
JAVA_HOMEconfigured appropriately
3. Solution
We recommend that you follow the instructions in the next sections and create the application step by step. However, you can go right to the completed example.
-
Download and unzip the source
4. Writing the Application
Create an application using the Micronaut Command Line Interface or with Micronaut Launch.
If you don’t specify the --build argument, Gradle is used as the build tool. If you don’t specify the --lang argument, Java is used as the language.
|
The previous command creates a Micronaut application with the default package example.micronaut in a directory named micronautguide.
5. OAuth 2.0 Dependency
To use OAuth 2.0 integration, add the following dependency:
<dependency>
<groupId>io.micronaut.security</groupId>
<artifactId>micronaut-security-oauth2</artifactId>
<scope>compile</scope>
</dependency>6. Micronaut AWS Secrets Manager Dependency
Add the following dependencies:
<dependency>
<groupId>io.micronaut.aws</groupId>
<artifactId>micronaut-aws-secretsmanager</artifactId>
<scope>compile</scope>
</dependency>
<dependency>
<groupId>io.micronaut.aws</groupId>
<artifactId>micronaut-aws-sdk-v2</artifactId>
<version>@micronaut-aws-sdk-v2Version@</version>
<scope>compile</scope>
</dependency>7. Distributed Configuration
7.1. Enable Distributed Configuration
Create a bootstrap.yml file in the resources directory to enable distributed configuration.
Add the following:
| 1 | Set the application name in bootstrap.yml instead of application.yml so that it is available when reading configuration from distributed sources.
properties |
| 2 | Set microanut.config-client.enabled: true which is used to read and resolve configuration from distributed sources. |
7.2. Clean up Application Configuration
If application.yml sets micronaut.application.name, remove it. You moved it to bootstrap.yml.
- micronaut:
- application:
- name: micronautguide7.3. Disable Distributed Configuration for Test
To disable distributed configuration for tests, create a bootstrap-test.yml file:
micronaut:
config-client:
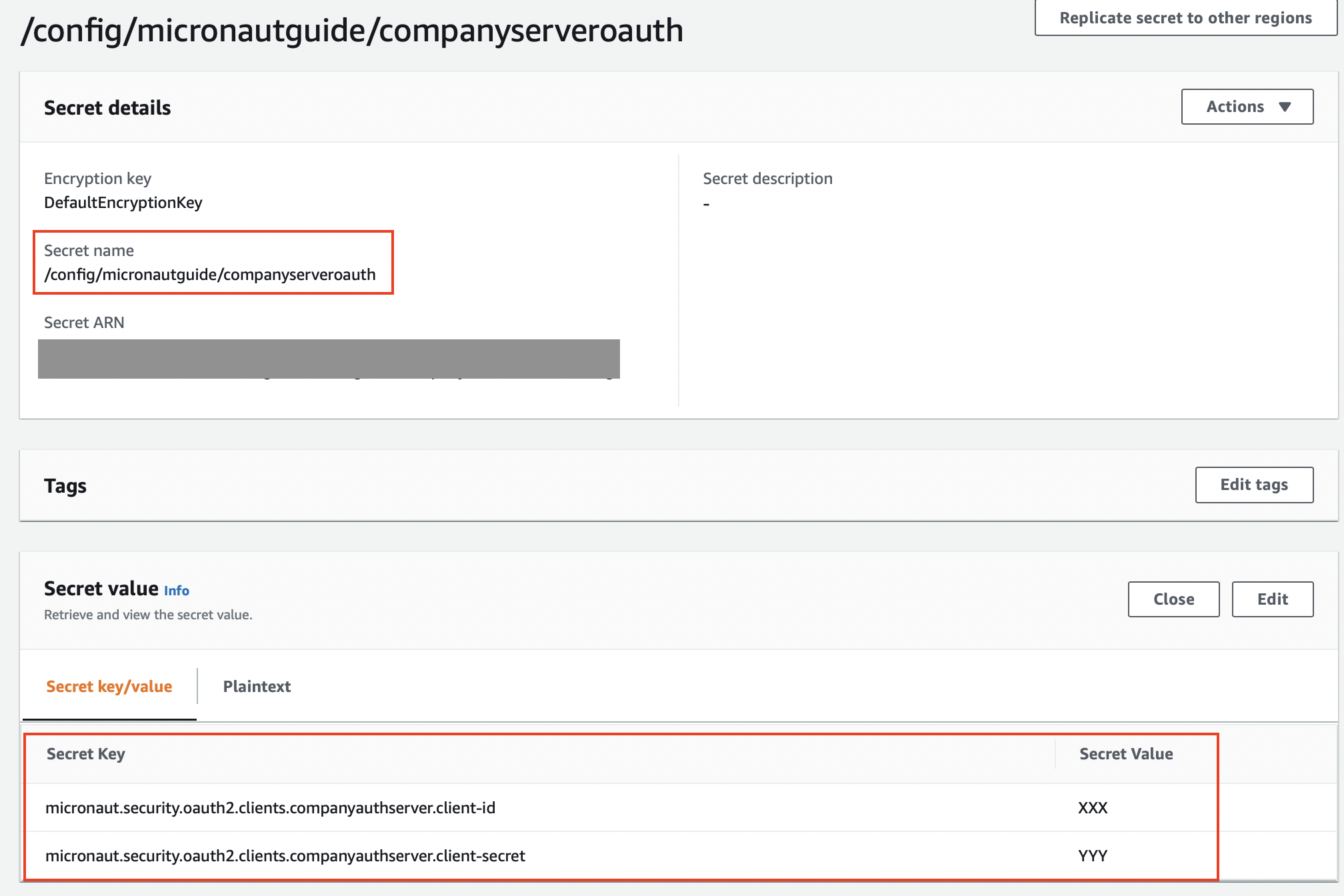
enabled: false8. Create Secret
OAuth 2.0 clients have a client id and secret property. We will save both in AWS Secrets Manager.
Create a Secret in AWS Secrets Manager
9. Controller
Create a controller which exposes the value read from AWS Secrets Manager.
package example.micronaut
import io.micronaut.security.annotation.Secured
import io.micronaut.security.oauth2.configuration.OauthClientConfiguration
import io.micronaut.security.rules.SecurityRule
import jakarta.inject.Named
import io.micronaut.http.annotation.Get
import io.micronaut.http.MediaType
import io.micronaut.http.annotation.Produces
import io.micronaut.http.annotation.Controller
@Controller
class ClientIdController(@Named("companyauthserver") oauthClientConfiguration: OauthClientConfiguration) {
private val oauthClientConfiguration: OauthClientConfiguration
@Secured(SecurityRule.IS_ANONYMOUS)
@Produces(MediaType.TEXT_PLAIN)
@Get
fun index(): String {
return oauthClientConfiguration.getClientId()
}
init {
this.oauthClientConfiguration = oauthClientConfiguration
}
}10. Logs
Add the following configuration to src/main/resources/logback.xml to get a more verbose output when the application starts up:
<logger name="io.micronaut.aws.distributedconfiguration" level="TRACE"/>11. Running the Application
To run the application, use the ./mvnw mn:run command, which starts the application on port 8080.
You should see traces such as:
12:26:56.602 [main] INFO i.m.context.DefaultBeanContext - Reading Startup environment from bootstrap.yml
12:26:57.554 [main] TRACE i.m.a.d.AwsDistributedConfigurationClient - application name: micronautguide
12:26:59.266 [main] TRACE i.m.a.d.AwsDistributedConfigurationClient - evaluating 2 keys
12:26:59.267 [main] TRACE i.m.a.d.AwsDistributedConfigurationClient - adding property micronaut.security.oauth2.clients.companyauthserver.client-id from prefix /config/micronautguide/
12:26:59.268 [main] TRACE i.m.a.d.AwsDistributedConfigurationClient - adding property micronaut.security.oauth2.clients.companyauthserver.client-secret from prefix /config/micronautguide/
12:26:59.268 [main] DEBUG i.m.a.d.AwsDistributedConfigurationClient - Property source awssecretsmanager with #2 items
12:26:59.268 [main] TRACE i.m.a.d.AwsDistributedConfigurationClient - property micronaut.security.oauth2.clients.companyauthserver.client-id resolved
12:26:59.268 [main] TRACE i.m.a.d.AwsDistributedConfigurationClient - property micronaut.security.oauth2.clients.companyauthserver.client-secret resolved
12:26:59.319 [main] INFO i.m.d.c.c.DistributedPropertySourceLocator - Resolved 1 configuration sources from client: compositeConfigurationClient(AWS Secrets Manager)
12:26:59.767 [main] INFO io.micronaut.runtime.Micronaut - Startup completed in 3378mscurl localhost:8080XXXX12. Generate a Micronaut Application Native Executable with GraalVM
We will use GraalVM, the polyglot embeddable virtual machine, to generate a native executable of our Micronaut application.
Compiling native executables ahead of time with GraalVM improves startup time and reduces the memory footprint of JVM-based applications.
Only Java and Kotlin projects support using GraalVM’s native-image tool. Groovy relies heavily on reflection, which is only partially supported by GraalVM.
|
12.1. Native executable generation
The easiest way to install GraalVM on Linux or Mac is to use SDKMan.io.
sdk install java 22.3.r11-grl| If you still use Java 8, use the JDK11 version of GraalVM. |
sdk install java 22.3.r17-grlFor installation on Windows, or for manual installation on Linux or Mac, see the GraalVM Getting Started documentation.
After installing GraalVM, install the native-image component, which is not installed by default:
gu install native-imageTo generate a native executable using Maven, run:
./mvnw package -Dpackaging=native-imageThe native executable is created in the target directory and can be run with target/micronautguide.
curl localhost:8080XXXX13. Next steps
Explore more features with Micronaut Guides.
Learn more about Micronaut AWS Secrets Manager integration.
Read about AWS Secrets Manager
14. Help with the Micronaut Framework
The Micronaut Foundation sponsored the creation of this Guide. A variety of consulting and support services are available.